By default, each organization's Umbrella dashboard instance logs all requests made by an identity. The level of logging for an identity's activity is set when you configure Centralized Settings > Advanced Settings. This setting is then shared with your organizations. By default, all requests are logged.
Logging options are:
Log All Requests—For full logging, whether for content, security or otherwise
Log Only Security Events—For security logging only, which gives your users more privacy—a good setting for people with the roaming client installed on personal devices
Don't Log Any Requests—Disables all logging. If you select this option, most reporting for identities with this policy will not be helpful as nothing is logged to report on.
Each of your organizations stores their activity logs to Cisco Umbrella's data warehouse. By default, Umbrella saves event data logs to Cisco's California location; however, you can change the location of the data warehouse from North America to Europe at any time. For more information, see Change a Data Warehouse Location.
The Cisco Umbrella Multi-Org console has the ability to upload, store, and archive traffic activity logs from your organizations' Umbrella dashboards to the cloud through Amazon S3. CSV formatted Umbrella logs are compressed (gzip) and uploaded every ten minutes so that there's a minimum of delay between traffic from the organization's Umbrella dashboard being logged and then being available to download from an S3 bucket.
By having your organizations' logs uploaded to an S3 bucket, you can then download logs automatically to keep in perpetuity in backup storage. Or, ingest the logs through your SIEM or another security tool to determine if any security events in your Umbrella logs coincide with events in other security tools.
Amazon S3 options:
A self-managed bucket—You own the Amazon S3 bucket, including its configuration and management.
A Cisco-managed bucket—Cisco owns the bucket and sets the configuration and management of it.
Extremely easy to set up—it only takes a couple of minutes—and easy to manage.
Included in the license cost for the Multi-org console, effectively making it free. Although having your own bucket is very inexpensive, the overhead of having to manage another bill can be prohibitive.
You cannot add anything to your bucket besides log files from your organizations and the bucket cannot be used by another application.
Some SIEM integration types may require advanced privileges for the user accessing the S3 bucket—beyond the basic Read permissions—and as such, may not work with the Amazon S3 feature.
You cannot get support from Amazon directly for advanced configuration assistance, such as automation or help with the command line.
Data can only be stored offline for a maximum of 30 days.
Update Billing Contact < Manage Logs > Enable Logging to Your Own S3 Bucket
Full administrative access to the Cisco Muti-org console
A login to AWS Management Console. If you don't have an account, Amazon provides free sign up for S3.
Note: Amazon requires a credit card in case your usage exceeds free plan usage.
A bucket configured in Amazon S3 to be used for storing logs. For more information, see Set up an Amazon S3 Bucket and Amazon S3 documentation.
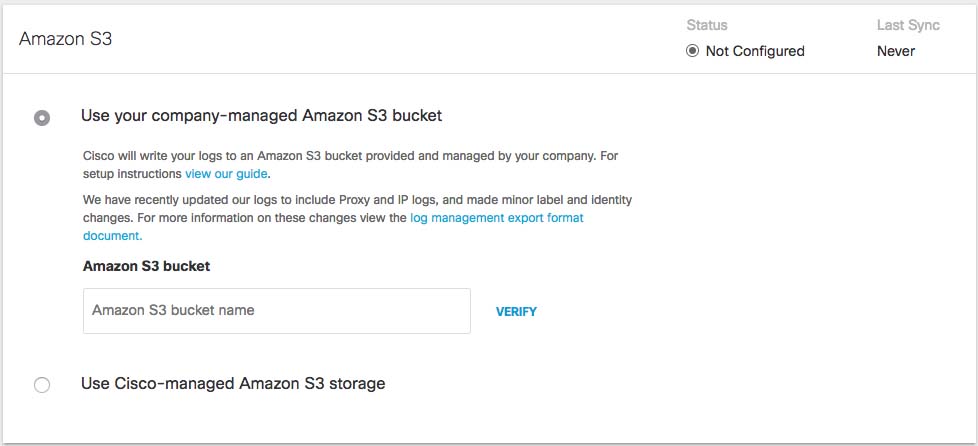
Navigate to Console Settings > Log Management and select Use your company-managed Amazon S3 bucket.
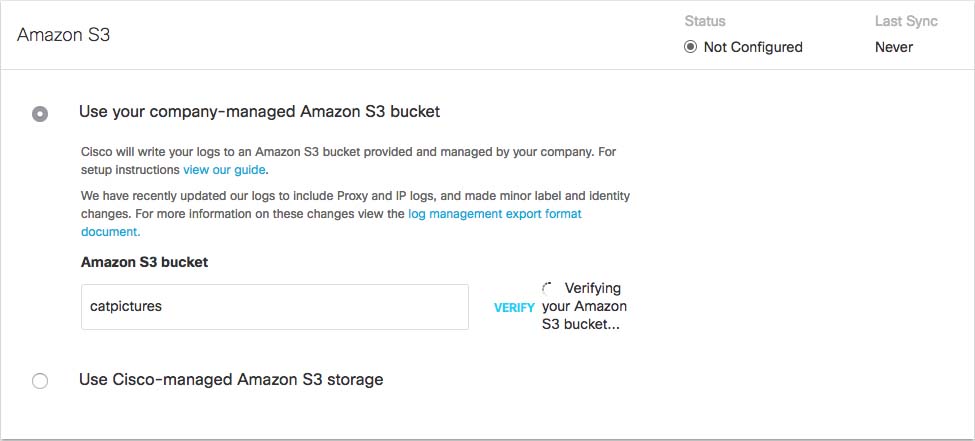
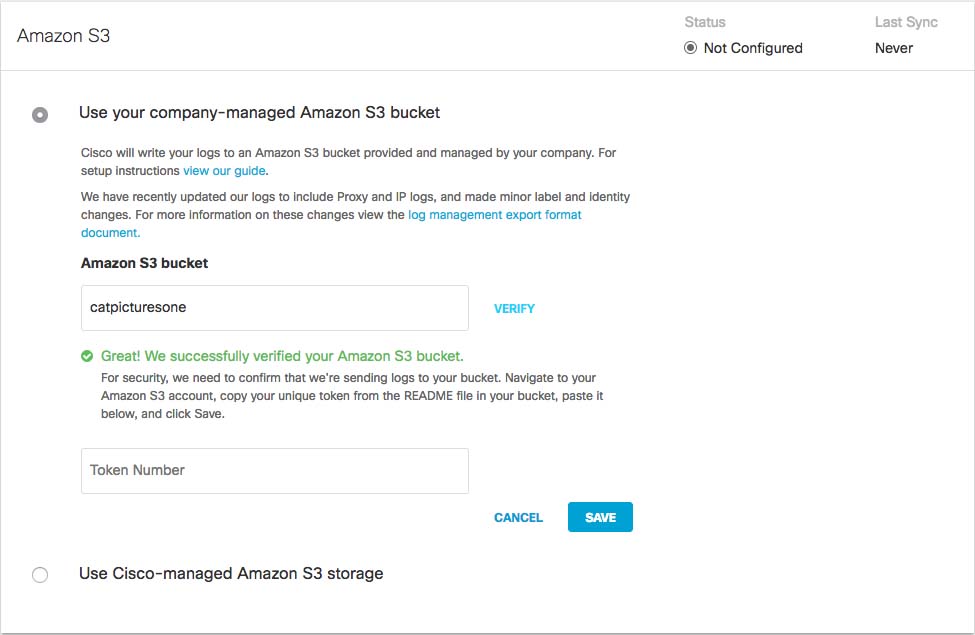
In the Bucket Name field, type or paste the exact bucket name you created in Amazon S3 and click Verify.
Umbrella verifies your bucket, connects to it, and saves a README_FROM_UMBRELLA.txt file to your bucket.
Open the README_FROM_UMBRELLA.txt file Umbrella saved to your bucket, copy and paste the token listed in it into Token Number, and click Save.
Manage Logs < Enable Logging to Your Own S3 Bucket > Set up an Amazon S3 Bucket
Before you can configure the Multi-or console to store your organization's logs to your own self-managed Amazon S3 bucket, you must first set up an Amazon S3 bucket. For information about how to do this, see Amazon's S3 documentation.
When setting up your bucket, you are required to add a bucket policy so that your bucket can accept uploads from your organizations' Umbrella dashboards. Copy and paste the following JSON string, which contains the preconfigured Umbrella bucket policy, into your Amazon S3 policy.
{
"Version": "2008-10-17",
"Statement": [
{
"Sid": "",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::568526795995:user/logs"
},
"Action": "s3:PutObject",
"Resource": "arn:aws:s3:::bucketname/*"
},
{
"Sid": "",
"Effect": "Deny",
"Principal": {
"AWS": "arn:aws:iam::568526795995:user/logs"
},
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::bucketname/*"
},
{
"Sid": "",
"Effect": "Allow",
"Principal":
{ "AWS": "arn:aws:iam::568526795995:user/logs" }
,
"Action": "s3:GetBucketLocation",
"Resource": "arn:aws:s3:::bucketname"
},
{
"Sid": "",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::568526795995:user/logs"
},
"Action": "s3:ListBucket",
"Resource": "arn:aws:s3:::bucketname"
}
]
} |
Enable Logging to Your Own S3 Bucket < Set up an Amazon S3 Bucket > Enable Logging to a Cisco-managed S3 Bucket
Reference Link : https://docs.umbrella.com/deployment-umbrella/docs/manage-logs |